Hacking has been around since early pre-alpha 2013, and while the early Alpha releases have dozens of commands you can use to achieve various effects, I’ve always considered the system a work in progress. There are more things that can be hacked, a few tweaks and changes to expect, and furthermore there are three major categories of hacks, and before Alpha 4 we’d only seen the first!
- Common hacks. Most of these are commands native to the system itself, functions and data that Operators and other robots need access to for their work. There are currently 54 of these.
- Unauthorized hacks. The topic of this post. Alpha 4 contains 11 of these.
- Unique hacks. NPCs will under special circumstances, or for plot purposes, give codes that can be used to achieve unique effects. These would of course always be entered manually. (There are actually a number of these coded in the game--originally added to test the implementation and ensure it works--but no way for players to discover them yet =p)
These three categories run the spectrum from common to obscure, in that order. So with Alpha 4 we’ve begun exploring the second category. Don’t worry, there are still more improvements and features to come in category 1.
The concept of “unauthorized hacks” was first introduced in relation to Garrison Access systems. These are hacks that attack the system itself or abuse it in some way, decidedly not what you’re supposed to be doing there. They are always entered manually--you’ll never see these listed like the others.
SPOILER WARNING: Beyond this point I’ll be revealing how to do each hack and how they work, even though you’re meant to learn all this via in-game lore! However, right now the necessary lore only exists for one of these hacks--respective lore for the others cannot be added until I create the part of the world where much of it will be found. Reading this will allow you to get around that temporary roadblock and check out this new content, but doing so doesn’t make it any less spoilery! Your choice :)
Unauthorized hacks can be divided into two sub-categories…
Trojans
With Trojans you install a program that runs on the target system to provide delayed or continuous long-term benefits. You’ll want to make sure the machine itself isn’t disabled, since that will of course render the Trojan useless. Once planted Trojans will continue to operate even if you are traced, however.
There are eight Trojans so far, affecting either Terminals or Garrison Access systems.
Terminal Trojans:
- Trojan(Track): Reports to you the current location of all robots within a square zone around the terminal, as if you were standing there with sensors and an Adv. Signal Interpreter. The area of effect is determined by the security level of the Terminal--higher tier systems have a greater range.
- Trojan(Assimilate): An Operator attempting to use this Terminal will instead be permanently converted to an ally (to join your personal hacker network :D).
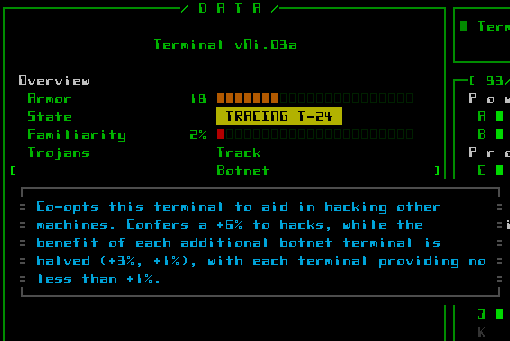
- Trojan(Botnet): As long as this terminal is active, it provides a bonus to both direct and indirect hacks at any other machine on the same floor. This effect stacks across multiple infected Terminals (with diminishing returns, in the same way multiple allied Operators stack). Build your own network!
- Trojan(Detonate): Sets all explosive machines within the Terminal’s zone of influence to explode immediately when your enemies pass by. Create your own oversized minefield!
Oops, Mr. Programmer, looks like you should’ve taken a left at the Subcomponent Replicator. (Nuclear Reactors previously infected by the Detonate Trojan--they glow yellow so you know/remember which ones they are).
Garrison Access Trojans:
- Trojan(Broadcast): Any squad dispatched from this garrison will have its type and composition reported to you immediately, and their location added to your intel database for reference.
- Trojan(Decoy): The next squad dispatched from this garrison will have its intended target switched to somewhere/something else at the last moment.
- Trojan(Redirect): All squads dispatched from this garrison have their target altered (more difficult than a one-off decoy).
- Trojan(Reprogram): The entire next squad to emerge will be converted to loyal followers!
Brute Force
A “brute force” hack completely disregards stealth and overwhelms the target system to achieve some effect, rendering it useless in the process (permanently locked). While brute forcing a system is guaranteed to attract attention, it’s quite easy to do and allows for some more extreme benefits.
Three different machines are currently susceptible to brute force attacks.
- Force(Extract): At any Scanalyzer, extract from the system’s memory a number of schematics for parts previously scanned by other robots. You can’t control the results, but if lucky it can be fairly useful.
- Force(Jam): Use this to prevent a Garrison Access system from opening the door for any squads trying to exit into the local area. This is the easiest way to cut off access from a garrison, but is also the most meddling from the enemy’s point of view, a third-rate option behind the much more difficult Seal hack, or simply blasting the Garrison Access system.
- Force(Overload): For those of you who don’t have much need of Fabricators, how about turning them into engines of destruction? :D This very unauthorized hack causes the machine’s EM imprinting system to go haywire, randomly zapping passing robots with corrupting beams of energy. Use only with intent to cause maximum chaos. And you’d better get out of the way! (This is the one which has already been added to the lore, so I didn’t really have to mention it here, but may as well for completeness sake--plus it’s the most fun =p)
There’s plenty of room for more unauthorized hacks in the future. This first batch was just a medium-sized “side project” alongside Garrison Access, to enable some additional strategic options for that machine.


6 Comments
Off the hook. Everything you do is so fresh, imaginative and well designed, I’m perpetually amazed. Can’t even think of anything to criticize lo these many posts. I probably asked this six months ago, but if so I forget: do you have a ballpark for release, like Fall 2016, or just 2016?
You are my design hero!
Well thank you! The blog sure doesn’t get as much comment love now that the forums are operational--much of the discussion happens elsewhere these days, but do drop a note from time to time if you can think of anything since the blog comments section has started to look a little lonely =p
I’m glad to have finally opened up for some design talk again in this series of Alpha 4 articles.
About the 1.0 release, I have sort of mentioned it in places, though never officially targeted a date because I want to ensure Cogmind meets my expectations for quality and content, which are incredibly high ;). Right now I have the FAQ saying “some time in 2016.” I’ll change that if I discover it’s simply not possible, but I think that really needs to happen, so it’s the ballpark I’m aiming for.
Developing a niche game full time is fairly expensive and risky, so I need to be realistic about how much resources are really available. Now that the game is on sale we have revenue, which is great, but having to devote time to maintaining the community is slowing progress, and combined with the confidence based on Cogmind’s popularity among players, I’m also willing to further extend development to include extra features. (This is already happening--I’m behind on the original roadmap, but ahead in terms of unplanned bonus features!) Overall what that means is that, in my mind, the potential release window keeps moving back from Q2 to Q3 to… Q4?
The foundation is solid, and already very playable and fun, but even after an epic amount of work (4,256 hours and counting, in fact), still an epic amount remains!
Still a long way off then. I hope you don’t get bogged down in feature creep, though with everything you’ve designed so far looking so promising it’s hard to complain.
Are you planning to go to Steam at some point? Other than the obvious revenue-splosion, it does allow for easy iteration and patching of released games.
One reason I’m not already playing Cogmind is I’ve gotten mired in several different turn-based Early Access games already. Trying to restrain myself from getting invested in more pre-releases.
Yeah, fairly long way, certainly longer than originally intended. Though as stated, due to extra features and community building, not poor development planning :P. I can accurately predict how long a given feature will take to implement, but factors like “how many features I’ll suddenly decide to add” are up in the air ;).
Feature creep is real, but not too big a threat. After all I do have a clear design doc and will not add any features that don’t support what I consider a fairly tight design. So there’s a limit to what can be added. That said, it turns out the foundation leaves quite a lot of room to add cool mechanics, and the most interesting content is still yet to come…
Steam is a definite yes. As is GOG. (Really, the questions you’re asking are on the FAQ, by the way ;)) I’ve even been reconsidering my approach to Steam. At first I wanted to launch there only for 1.0, but for several reasons I may start there with EA, most importantly if it looks like development is dragging on too long. Just an idea; we’ll see later next year.
I’m also trying to leave some more of the optional features until after 1.0, so meaningful updates can continue beyond that point. To an extent. There are other games to make!
Shameless Necro-post.
Found this today, still super useful!
Hehe, necrocommenting is fine :). And glad you found it useful! Technically all these can be discovered in game, but if you’re not averse to spoilers (apparently not :P), yet more of these have been added over the past couple years since this original post, and players have collected them on the wiki.