hack /hak/ v. Gain unauthorized access to a system.
For the past several weeks development has mostly focused on what can be considered the “other half” of the game. Aside from exploring the map, fighting robots, and re-building yourself, an entirely new component unseen in the 7DRL prototype is now being integrated into the game: Hacking. (I briefly touched upon hacking earlier with the introduction of machines.)
This is both wonderful and scary at the same time. Wonderful because there will be a whole range of new ways to interact with the world, and scary because it can be a pretty major part of the game but was never prototyped!
This is a mockup of the hacking interface as it could appear over the map:
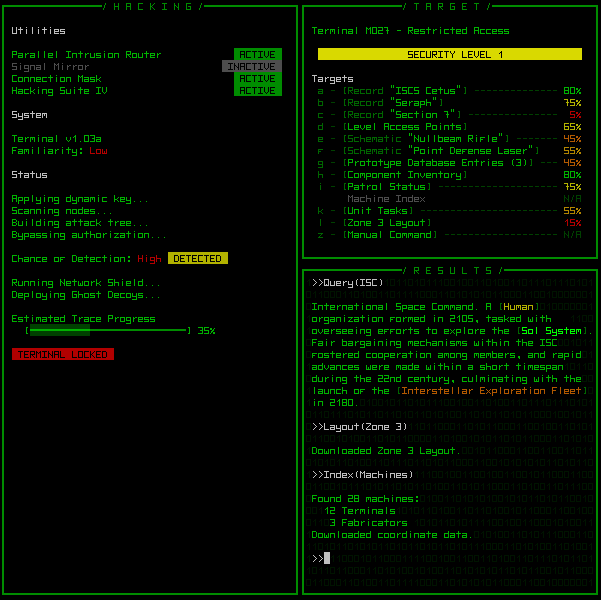
Left: First console to appear, showing general information and the progress of the hack. Top-right: List of known targets to hack from the current machine. Bottom-right: Commands entered and their results.
So where does hacking fit into the game?
Firstly, most of the story is presented through data files accessible at terminals, essentially making it optional for those who care to know what the heck is going on (trust me, when you find the cave systems, or stumble across hidden research labs, you’ll want to know at least a little of what’s going on).
From a gameplay perspective, hacking opens up more strategic options through the various functions machines are capable of. Everything they can do is closely integrated with other parts of the game. In general machines enable you to gather information, manipulate the environment, and provide tools to augment your capabilities.
You can do as much, or as little, hacking as you want depending on your needs and style. Following posts will explore the interface and mechanics in more detail. (I’ve tried to keep the system simple, but it turns out there really is still a lot of detail in there…)


4 Comments
so does the tracking happen in realtime like in uplink or is it turnbased?
Good question, I should’ve addressed that aspect in the post. Everything in the game will always be turn-based; there will be no real-time elements. While hacking, it’s your actions that advance the state, so you can sit around and think about what you want to do as long as you like, or even get up and go get a coffee, have a chat with your neighbors, or whatever, and the system will wait for you :). The next post will go through the entire process.
Since it hasn’t been prototyped yet, the system will likely require some adjustments once we get to playtesting, but for now I’m just steamrolling through development to get the framework done. We’ll see how it turns out.
(Additional note: While hacking a machine, action on the map does not progress at all, since all hacking actions are considered essentially instantaneous. This may work differently for hacking robots, but that hasn’t been fully planned yet.)
ohh this makes me dream of an xcom rogue operative hacking into a high security research lab! ^_^
Hehe, totally. Hold that dream. It could one day become a reality when some of the new features developed for Cogmind translate back to a bigger better X@COM. Not sure I’d go so far as to include a very detailed menu system and separate console for agent hacking use, but X@COM already supports scripting that enables things like hackable environmental props, so it will definitely come to be in one form or another.